GitLab, one of the biggest competitors of Microsoft’s GitHub, employs more than 1000 employees and worth about $3 billions.
Most of us, and probably GitLab management, would expect that its employees, most of them are experienced software developers, would be aware of the cyber threats outside and will know how to safely use the web.
So… According to Gitlab tests, phishing can get even the best!
Phishing is a cyber attack that involves emails, phones, text messages for someone who pretends to be a legitimate organization. In those attacks, the attacker extracts personal information.
And back to Gitlab. The company made some very common tests on its workers.
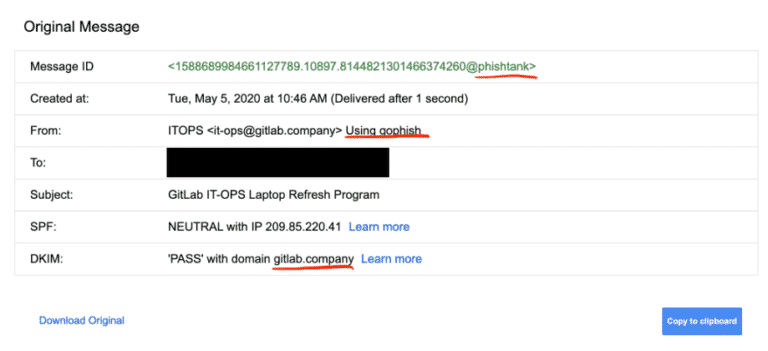
First of all, they purchased a domain named – gitlab.company, set a G-suit account and even had SSL certificate.
GitLab sent personal emails for specific member employees (this attack is called Spear Phishing) and sent an email about upgrading a laptop – something every employee waits for.
This is the mail –
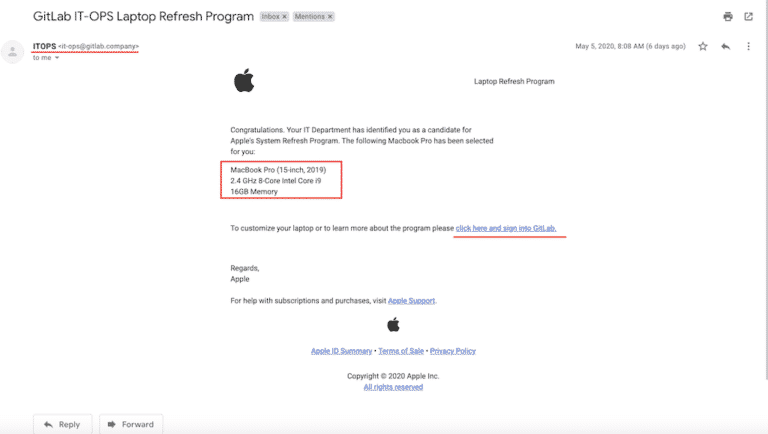
The email, which was sent by the fake IT department looks pretty much like an email made by Apple, which supposed to arouse suspicion. At the end of the emails, they attached a link to get more details on the replacement.
GitLab’s team left clues that were available in a click of a button –
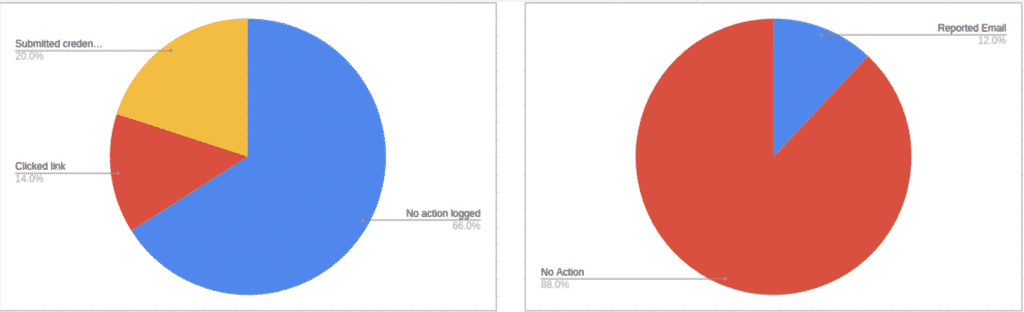
The results were pretty bad… Out of 50 employees, 17 of them clicked the link, but this is not the bad part… 10 of those 17 employees exposed their credentials in this process.
That being said, 20% of the test subjects handed their credentials to hostile attacker which could lead to major cyber attack on GitLab.